Physical Cybersecurity: Flipper Zero, Pegasus Spyware, and Shielding Engineering
Modern hyper-connectivity has blurred the line between digital cybersecurity and physical security. The proliferation of IoT, keyless vehicle systems, and RFID payments have expanded the attack surface to unprecedented levels. The convenience of wireless has introduced critical vulnerabilities that are now systematically exploited.

At Eldelirio.es, we dissect the current state of physical cybersecurity. First, we analyze the tools attackers use today and the real damage they can cause. Next, we detail how to face these threats through material engineering solutions, from RFID wallets to Faraday bags and selective blocking sleeves.
1. The Infiltration Arsenal (Hardware and Software)
The accessibility of pentesting hardware and military-grade spyware has transformed the global risk landscape. Capabilities once exclusive to intelligence agencies are now available to cybercriminals and executed invisibly.
A. The Anatomy of the Flipper Zero and the Hacker Ecosystem
The Flipper Zero has emerged as the most iconic and controversial device in the field of wireless security. From a technical perspective, it is a multi-protocol transceiver and analyzer capable of operating across multiple electromagnetic spectrums.
Its native capabilities allow it to interact with:
-
Sub-1 GHz Frequencies: To clone and emulate garage door controls and legacy IoT systems that transmit static codes.
-
Low-Frequency RFID (125 kHz): Allows for the passive excitation of corporate or hotel access cards, reading their non-encrypted identifier, and emulating them in seconds.
-
High-Frequency NFC (13.56 MHz): To read and interact with modern bank cards and biometric passports.
Myth vs. Reality: Most viral videos showing the Flipper Zero opening cars are staged. The factory device has hardware and firmware restrictions that prevent it from bypassing modern vehicle security. However, the real risk appears when installing third-party firmware (like Unleashed or Xtreme) and external antenna modules.
With these modifications, a “souped-up” Flipper Zero can clone encrypted high-frequency access cards (Mifare), intercept smart meter communications, act as a BadUSB to inject malware into unattended computers in a matter of seconds, or, most worryingly, execute attacks against vehicles. We will detail how these vehicle attacks work in Section 2.
B. State Surveillance: The Pegasus Case
The most insidious threat vector in 2026 is not physical theft, but the total compromise of the device through spyware like Pegasus (developed by NSO Group). The severity of this cyberweapon was exposed globally after its confirmed use against high-profile targets: from human rights defenders and the inner circle of murdered journalist Jamal Khashoggi, to heads of state like Emmanuel Macron and multiple political leaders in espionage scandals involving the Spanish government and the infamous Catalangate.
Once infected, often through “zero-click” exploits requiring no interaction from the victim, Pegasus converts the smartphone into a total surveillance device. It can remotely activate the microphone and camera to listen to face-to-face conversations (a technique known as hot mic’ing), access end-to-end encrypted chats (Signal, WhatsApp), passively track GPS location, and extract passwords from secure keychains. Since these attacks are almost impossible to prevent with standard software alone, entities like Amnesty International and Citizen Lab recommend the absolute physical isolation of the device in a Faraday bag during key meetings, especially for journalists, dissidents, and executives on sensitive trips.
2. Anatomy of the Attack: Vectors and Consequences
With the lethal tools just exposed operating at full capacity, the theoretical threat becomes a tangible reality. Below, we detail how these silent attacks materialize on the ground and the logic behind their devastating consequences.
A. Vehicle Theft I: Classic Systems and “RollJam”
For cars that rely on pressing a button on the remote (Rolling Codes), the star technique is the RollJam. How does it work? The victim presses the remote control to open the car, sending “Code 1”. The attacker uses a modified Flipper Zero or similar device to block (jam) the signal so it doesn’t reach the car, while simultaneously recording it. The user, seeing the car didn’t open, presses the button again, sending “Code 2”. The attacker intercepts “Code 2”, but this time the device instantly re-transmits the retained “Code 1”. The car opens, and the victim walks away assuming the remote just failed the first time. The attacker now possesses the pristine, unused “Code 2”, which is completely valid to steal the vehicle later without triggering alarms.
B. Vehicle Theft II: “Keyless” Systems and “Relay Attacks”
While RollJam comes into play when the user actively presses the button on the remote, the Relay Attack is designed specifically to steal modern vehicles with “Keyless Entry” (or Smart Key) systems. Instead of hijacking temporary signals, it takes a direct path: brutally tricking the car’s physical proximity sensors. It is the fastest and most widely used vector by organized gangs:
- Interception and Bridge: An attacker next to your front door captures the signal continuously emitted by your key resting on the hallway console.
- Signal Shot: Using backpacks or briefcases with hidden antennas, they amplify and “shoot” that signal to their accomplice, who is waiting and grabbing the door handle of your parked car on the street.
- Ghost Start: The car reads the amplified response, believes its original owner is standing there with the key in hand, and unlocks and starts in a mere 15 seconds without using brute force or breaking a single window.
C. Invisible “Skimming” and Identity Theft
“Skimming” involves stealing data wirelessly simply by bringing a hidden reader close to the victim. While walking through crowded environments—like an airport terminal or a packed subway car—an attacker with a Flipper Zero or a high-power RFID reader hidden in a backpack can remotely “wake up” the cards and passports we carry in our pockets.
With a simple invisible sweep, the attacker can:
- Extract payment data: Capture the number and expiration date of contactless credit cards, and sometimes even the history of recent transactions.
- Clone credentials: Copy corporate access badges or hotel key cards to physically enter restricted buildings without forcing locks.
- Steal biometric data: Extract the photograph, name, and date of birth from chips embedded in modern passports (e-Passports).
The real danger happens after this massive data harvesting. Criminal networks feed these scattered fragments of information (a name from a passport, a birth date from an ID, a card number from another victim) into powerful Artificial Intelligence models. These engines mass-produce Synthetic Identities: “Frankenstein” profiles that mix real and fabricated data. With these, they manage to bypass bank algorithms to open accounts, request loans, and vanish without a trace.
D. Encryption Evasion and Absolute Control
All the aforementioned gadgetry (like stealing cars undetectably or emptying balances with clones) pales in comparison to how state-grade spyware operates in this same ecosystem.
As we saw with Pegasus, once your device is breached at the operating system level (kernel), your security tools become meaningless. It is useless to securely use applications like Signal or WhatsApp with end-to-end encryption, as the attacker doesn’t waste time decrypting packets in transit across the internet; they simply read the screen and log the keyboard directly from your phone before it gets encrypted (on-device interception). Faced with such a deep compromise, where the invader is the very device you trust, the only real and effective mitigation is not digital, but material: the immediate physical destruction of the radio frequency link through electromagnetic isolation (Faraday Cage).
3. The Science of Invisibility: Physical Foundations
Faced with attacks that operate invisibly through radio waves, conventional software cybersecurity is not enough. The real defense lies in materials physics.
The Faraday Cage as the Definitive Physical Control
A professional Faraday bag is not just an accessory, but a physical control that operates below the level of the operating system or firmware. While “airplane mode” can fail or be manipulated by spyware so that the phone appears disconnected while still emitting Bluetooth or Wi-Fi signals, a Faraday cage imposes real electromagnetic isolation.
To neutralize spyware, the shielding cuts the communication link necessary for the attacker to send remote wipe commands or receive live transmissions from the compromised microphone. It not only blocks data outgoing but prevents the device from receiving new control commands.
4. Shielding Guide: Protection Levels
Below, we detail the three major lines of commercial defense designed under engineering standards to combat these risks.
Level 1 Defense: Against Skimming (RFID Wallets)
To neutralize the physical threat of RFID readers (125 kHz) and NFC scanners (13.56 MHz) hidden in backpacks, classic leather wallets are being replaced by metal exoskeletons that absorb and dissipate the attacker’s electromagnetic energy.
| Brand | Approach and Design | Access Mechanism | Capacity |
|---|---|---|---|
| Ridge | Extreme minimalism. Solid Aluminum, Titanium, or Carbon Fiber plates under elastic tension. Total physical shield. | Manual push via notch. | 1 to 12 cards |
| Ekster | High tech. Recycled aluminum cavity. | Side trigger that ejects cards in a tiered fan. | Up to 12 cards (depending on model) |
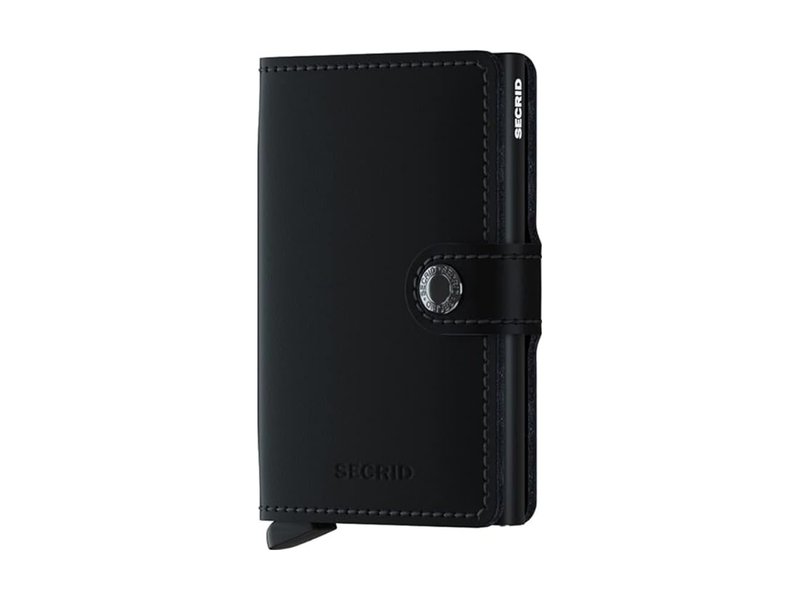
| Secrid | Premium leather goods. Extruded aluminum Cardprotector core in a single piece without fragile joints. | Robust mechanical action bottom trigger. | 6 to 16 cards (depending on model) |
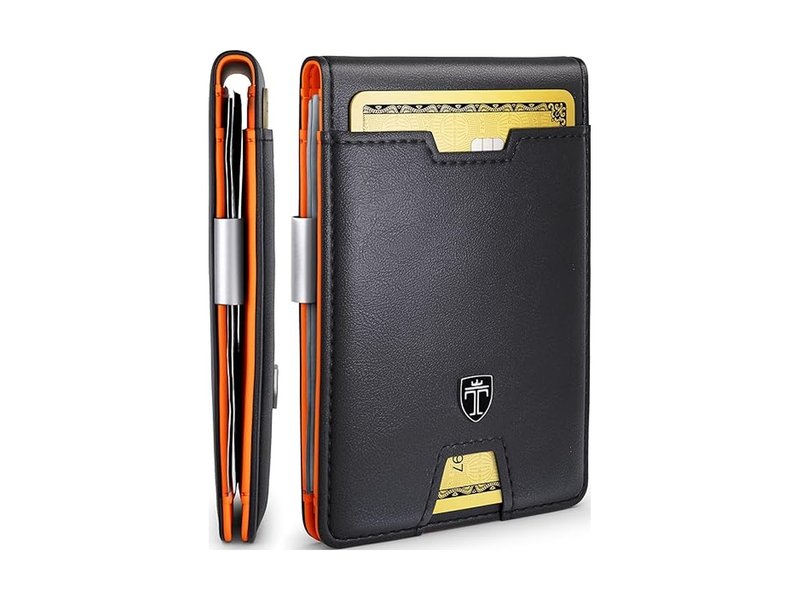
| Travando | Quality-price ratio. Traditional folding design (bifold) lined with RFID-certified fabric. | Book opening with exterior notch for quick extraction. | Up to 11 cards (depending on model) |
| Bewmer | Urban versatility. Rigid aluminum central box with synthetic leather coatings. | Automatic pop-up system with anti-fall mechanism. | 6 to 9 cards (with zipper) |
| Ögon Design | Hermetic security (European pioneers). Sealed aluminum “safe-box” design without fragile elastics. | Exterior button that unfolds the interior like an accordion. | Up to 10 cards (depending on model) |
Correct Use: Empirical tests show that rigid plate exoskeletons (like Ridge, Ekster, or Secrid) or safe-box designs (Ögon Design) provide 100% baseline physical effectiveness. Traditional leather or bifold wallets rely entirely on a thin internal mesh. If you opt for leather, demand brands like Travando that subject their fabrics to laboratory certifications (e.g., German TÜV institute). Cheap knockoffs or imitations often fail quickly due to signal leakage through their seams.
How can you test your wallet at home? Download a free app like NFC Tools on your smartphone. Put your contactless card inside the closed wallet and tap your phone against it. If the phone does not vibrate or detect a chip, your shielding is working perfectly. (Technical note: Your phone’s NFC protocol operates under the 13.56 MHz RFID standard, identical to payment terminals and the readers used by criminals. Blocking one means isolating the other).
Level 2 Defense: Against Tracking and Vehicular Theft (Faraday Bags)
To thwart Sub-1 GHz cloning (common in garage remotes), vehicular Relay Attacks (Keyless), or silent accesses via mobile antenna like Pegasus, the only defense is total spectral isolation. Enclosures designed under military standards (MIL-STD-188-125-2) are required, reaching attenuations of up to 100 dB+ (reducing any radio wave 100 million times).
Standards and Conductive Fabrics
-
Mission Darkness Non-Window Faraday Bag (MOS Equipment): The reference brand for police forensic analysis. Their mobile and tablet bags use TitanRF™ fabric, a non-sewn copper and nickel composite that eliminates signal leakage points. Their seams are thermally welded, eliminating microscopic holes where 5G or Bluetooth would leak.
-
SLNT Faraday Sleeve (Silent Pocket): Focused on executive everyday carry (EDC). Employs Multishield® technology, which layers materials to resist fatigue and ensure total isolation. Its use forces the mobile phone into biological hibernation, preventing location tracking and Wi-Fi/Bluetooth attacks while significantly extending battery life.
-
Mission Darkness Keyfob Shield (Keyfob and Crypto Custody): This miniature form factor is used to block vehicle theft via Relay Attack, and is also recommended by institutions to secure cold Bitcoin hardware wallets (Ledger, Trezor) against sophisticated thermal or radio-electronic side-channel attacks initiated just meters from the safes.
-
Lanpard Keyless Pouches (Value for Money): The most popular and affordable alternative. While they don’t use military-grade standards like SLNT, these small twin pouches perfectly serve their purpose as an entry-level radio frequency (Sub-1 GHz) barrier to stop thieves from cloning your car key from your front door.
Level 3 Defense: The Future of Selective Blocking (FSS Sleeves)
The great challenge of Faraday bags is their binary nature (“all or nothing”). If you keep your phone in a bag to protect yourself from NFC passport scanning or tracking, you lose 5G coverage and notifications.
To solve this, the major industry innovation (led by materials labs and companies like OSOM Products) are Frequency Selective Surfaces (FSS).
Instead of solid metal, the sleeves use resins with micron-scale printed geometric patterns (such as crosses and rings). This topology acts as an intelligent filter:
-
Stopband: The sleeve relentlessly blocks the 13.56 MHz frequency (NFC/RFID), “blinding” stealth readers and devices like the Flipper Zero that attempt to communicate with the chips located inside the phone.
-
Passband: Simultaneously, the matrix allows the spectrum from 700 MHz to 3.5 GHz (5G, LTE, and Wi-Fi networks) to pass through the material freely.
This advance allows for the massive civil adoption of physical cybersecurity: the user maintains their phone line, receives emergency calls and emails, while being completely immune to the silent hijacking of short-range chips residing in their device.
5. Conclusion: The Physical Frontier
In an ecosystem where your vehicle, your money, and your identity are permanently wandering emitting signals in the invisible spectrum, software is no longer enough. Building digital encryption protocols is useless if the criminal intercepts the physical wave at its root or compromises your operating system as we saw with Pegasus. Protecting your radio frequencies is not an act of paranoia; it is the new sanity.
At Eldelirio.es, we know that threats evolve, but the laws of physics are immutable. A structural shield never expires and cannot be hacked via a malicious patch. Automated tracking and attacks are not going to stop. You decide what signals enter and leave your pockets.
[ END OF TRANSMISSION ]